Favorites
Customize ESPN
ESPN Sites
ESPN Apps
An advanced analytics look at Panthers-Bucs, Seahawks-49ers, more
Next Gen Stats looks at Baker Mayfield holding the ball too long, the Seahawks' pressure, and Zay Flowers' success vs. man.

Our guide to every Week 18 game: Matchup previews, predictions and more
Must-win NFC showdowns? No. 1 seeds on the line? We have everything you need for Week 18.

TOP HEADLINES
LOOKING FOR A NEW HOME
TRANSFER PORTAL IS OPEN
College football transfer portal: Tracking who's on the move
The transfer portal opened on Jan. 2. We're keeping tabs on players who enter.

Thamel on transfer portal: It's a ridiculous 'free-for-all' right now


NFL SCOREBOARD
TOP MOMENTS FROM MAYO BOWL
Koredell Bartley takes kickoff return for 100-yard TD in Wake Forest’s win

'We're ready for the mayo bath': Wake Forest coach and family celebrate win

BOWL GAME SCOREBOARD

NBA SCOREBOARD

MUST-SEE FROM WEEK 1 OF TGL
TGL best moments: Boston Common earns first win in team history
Boston Common Golf beats Los Angeles Golf Club to open the season with its first win in team history.


BREAKING DOWN THE CFP
CFP quarterfinal takeaways: Ole Miss' wild upset, Indiana's dominance and more
The semifinals are set. We go inside every quarterfinal game to see how we got our final four.

CFP semifinals first look: Previewing the penultimate round
How each team can win its semifinal game, plus key players and what we learned from the quarterfinals.

Top Headlines
- Sources: Ole Miss QB Simmons plans portal entry
- Rangers stay perfect outdoors, win at Marlins' park
- Finland stuns U.S. in world junior hockey quarters
- Unbeaten Huskers to fans: Quit storming court
- QB Reed says he'll return to Texas A&M for '26
- Sources: Sorsby, top portal QB, to visit TTU, LSU
- Steelers' Watt feels 'no limitations,' set for return
- Diggs, Barmore decline to discuss facing charges
- 🍼 Jordan Love, Ronika Stone expecting 1st child
Customize ESPN
ICYMI
Ole Miss survives onside kick, last-play laterals to defeat Georgia
After a safety leaves one second on the clock, Georgia recovers an onside kick but fails to score on the final play in Sugar Bowl loss to Ole Miss.
NFL Playoff Machine
Mark J. Rebilas/USA TODAY Sports Simulate playoff matchups
Predict playoff pairings by selecting the winners of the remaining regular-season games to generate potential scenarios.
Sounding Off
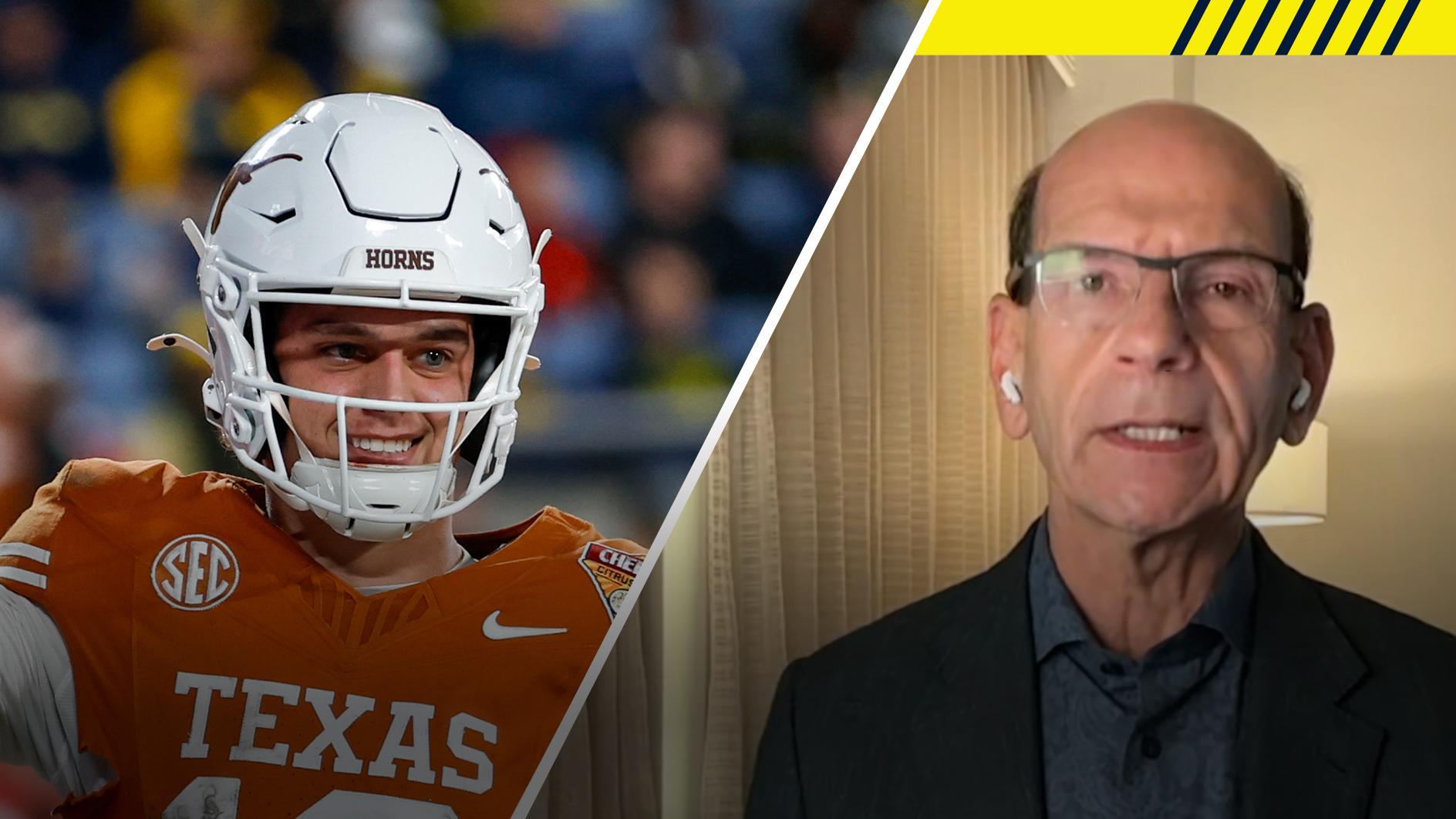
Finebaum: Arch Manning will win the Heisman next year
Paul Finebaum joins "Get Up" to discuss Arch Manning's performance this season and what it means for his future.
Trending Now
ESPN NBA Power Rankings: Where all 30 teams stack up heading into the new year
Our NBA insiders lay out where all 30 teams stack up in the last power rankings of 2025.
Rich Graessle/Icon Sportswire Concerning weaknesses, flaws for 2025 NFL playoff teams
We found fatal flaws for all 12 clinched teams in the playoff field, plus the AFC North and NFC South teams trying to join them entering Week 18.
Illustration by Masa 2025 NFL playoff picture: Updated odds, seeds, draft order
We are following the 2025 NFL season's playoff picture. Here's how things look right now for wild-card spots, division races and even the draft order.
Vaughn Ridley/Getty Images Our favorite MLB games of 2025: World Series Game 7 and more
From playoff thrillers to epic individual achievements, these are the moments we'll remember for decades to come.
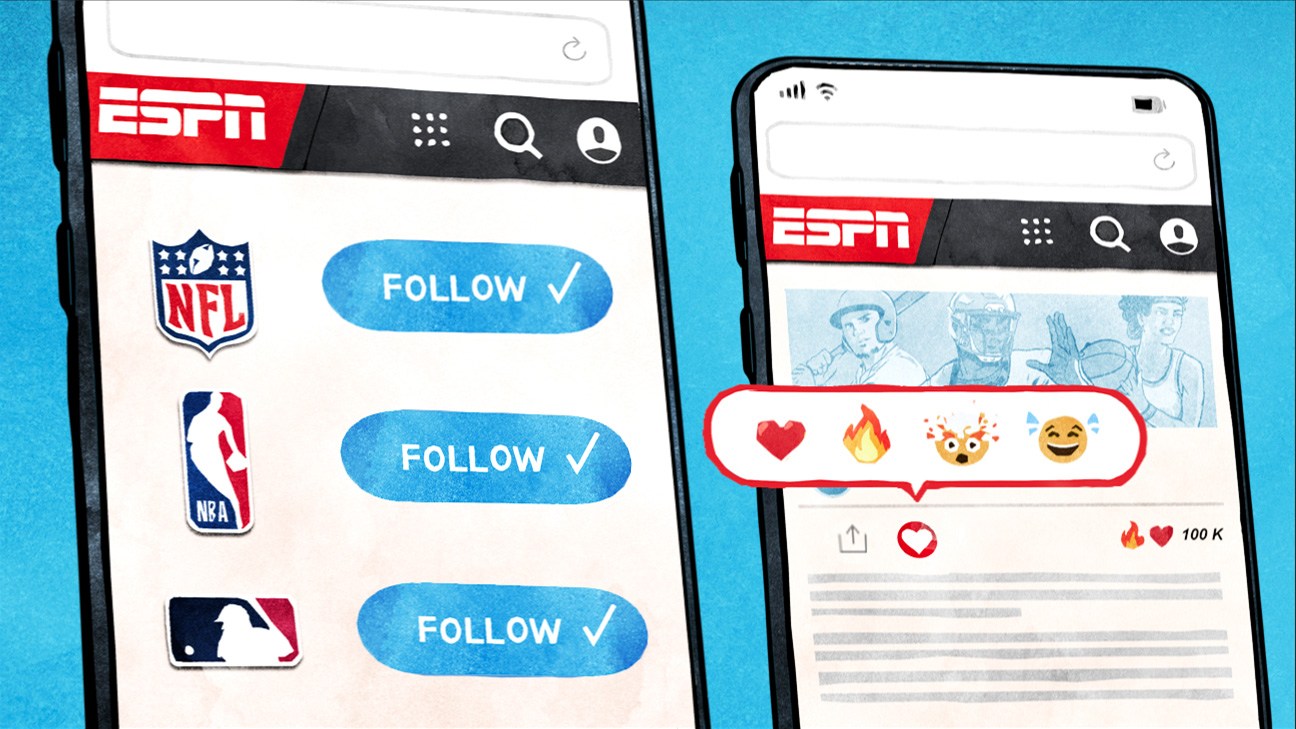
Get a custom ESPN experience
Enjoy the benefits of a personalized account
Select your favorite leagues, teams and players and get the latest scores, news and updates that matter most to you.